Top secret: Fraud detection with Elastic Preliminary Disclaimer: The title “top secret” can be interpreted in various ways. To clarify,…
Getting the most out of Generative AI with Elastic. Generative AI, or Gen AI, is reshaping the technology landscape. Just…
Post ElasticON: Cybersecurity & AI Organizations face the daunting task of safeguarding their digital assets against a myriad of…
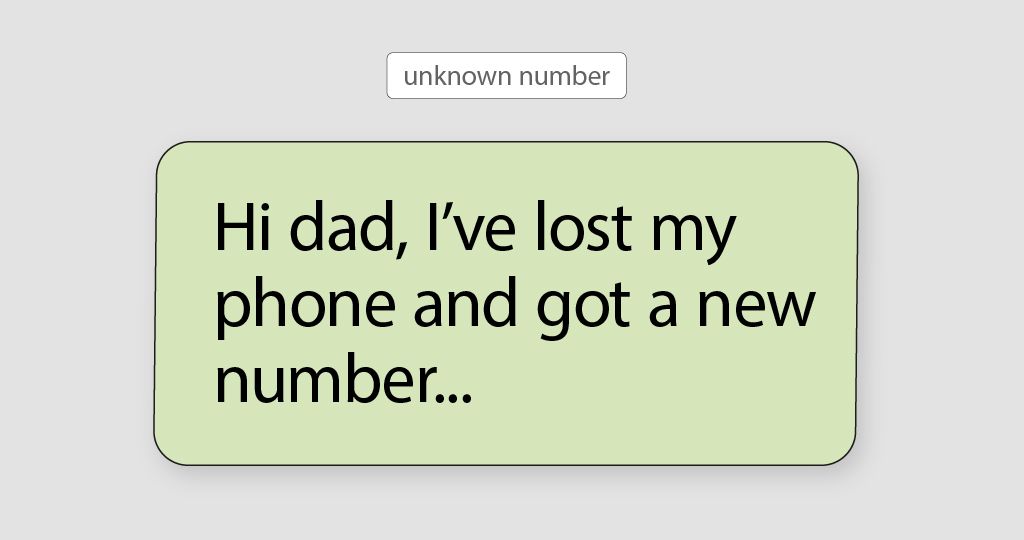
hacking test(s): obtaining user data via known apps introduction Computers are an integral part of our daily lives, but do…
RANSOMWARE: PREVENTING WANNACRY ATTACKS WITH ELASTIC INTRODUCTION In this blog post, we will explore how Elastic Security handles a WannaCry…
Cybersecurity trends in 2023 The digital world keeps broadening as we migrate more and more to the Cloud, Private cloud,…
Elastic Security at ElasticOn Amsterdam At ElasticOn Amsterdam, the security team reaffirmed their ambition to create an Elastic Security solution…